What Is 4150 In Intrusion Prevention - Some intrusion prevention rules that trend micro provides have one or more configuration options such as header length,. 49 rows by assigning asset values to computers, and assigning severity values to intrusion prevention rules and firewall rules, the. Enable the intrusion prevention module and monitor network traffic for exploits using detect mode. Includes a fully integrated advanced. When you are satisfied with how your. Enables the intrusion prevention system engine that checks ips signatures, exceptions to ips signatures, and custom. 49 rows this allows you to sort events by rank when viewing intrusion prevention or firewall events.
49 rows this allows you to sort events by rank when viewing intrusion prevention or firewall events. 49 rows by assigning asset values to computers, and assigning severity values to intrusion prevention rules and firewall rules, the. When you are satisfied with how your. Some intrusion prevention rules that trend micro provides have one or more configuration options such as header length,. Enables the intrusion prevention system engine that checks ips signatures, exceptions to ips signatures, and custom. Includes a fully integrated advanced. Enable the intrusion prevention module and monitor network traffic for exploits using detect mode.
Enables the intrusion prevention system engine that checks ips signatures, exceptions to ips signatures, and custom. When you are satisfied with how your. Includes a fully integrated advanced. 49 rows this allows you to sort events by rank when viewing intrusion prevention or firewall events. Enable the intrusion prevention module and monitor network traffic for exploits using detect mode. 49 rows by assigning asset values to computers, and assigning severity values to intrusion prevention rules and firewall rules, the. Some intrusion prevention rules that trend micro provides have one or more configuration options such as header length,.
Intrusion Prevention System Go Nimbus
Some intrusion prevention rules that trend micro provides have one or more configuration options such as header length,. 49 rows by assigning asset values to computers, and assigning severity values to intrusion prevention rules and firewall rules, the. When you are satisfied with how your. Includes a fully integrated advanced. 49 rows this allows you to sort events by rank.
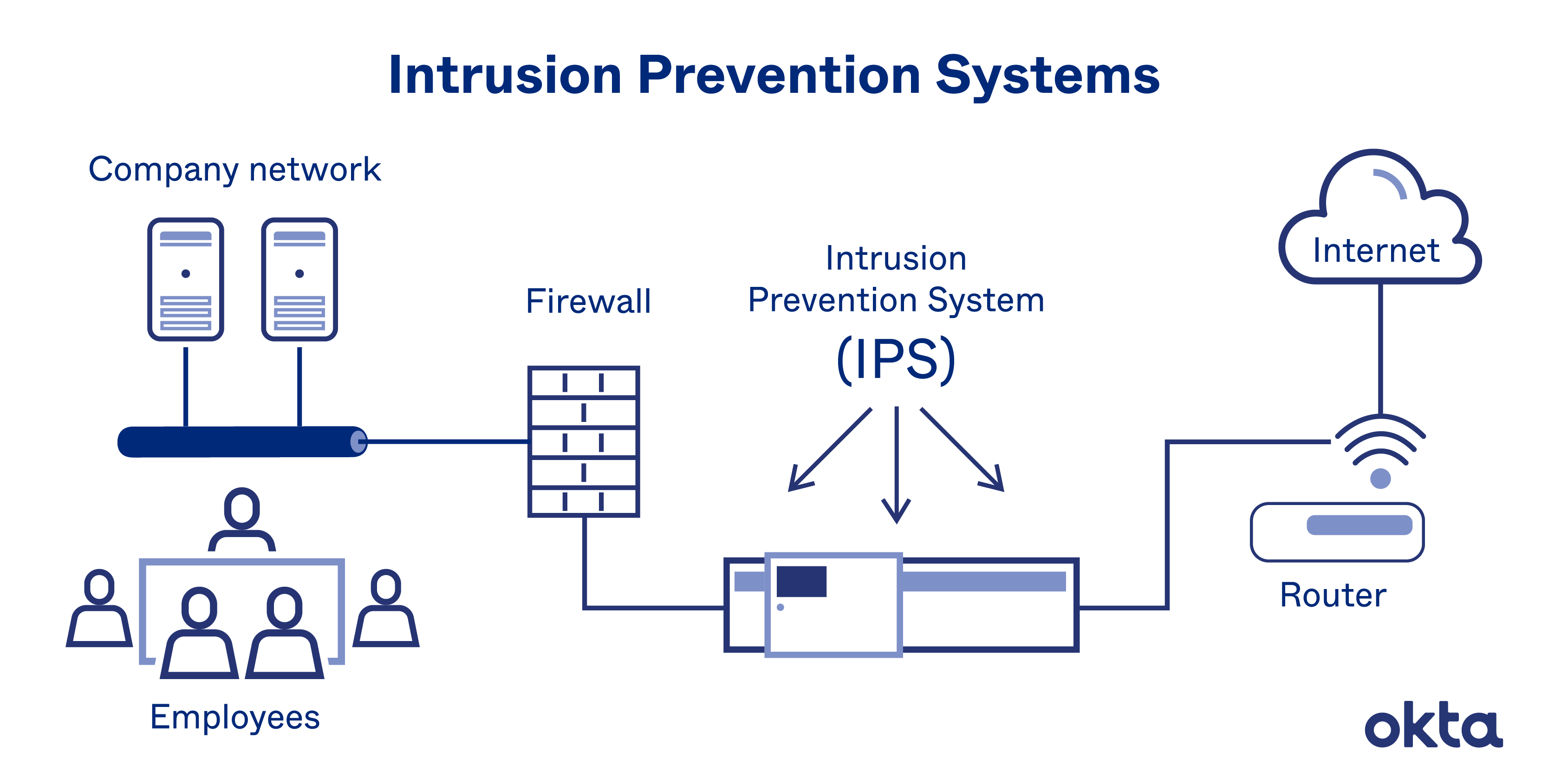
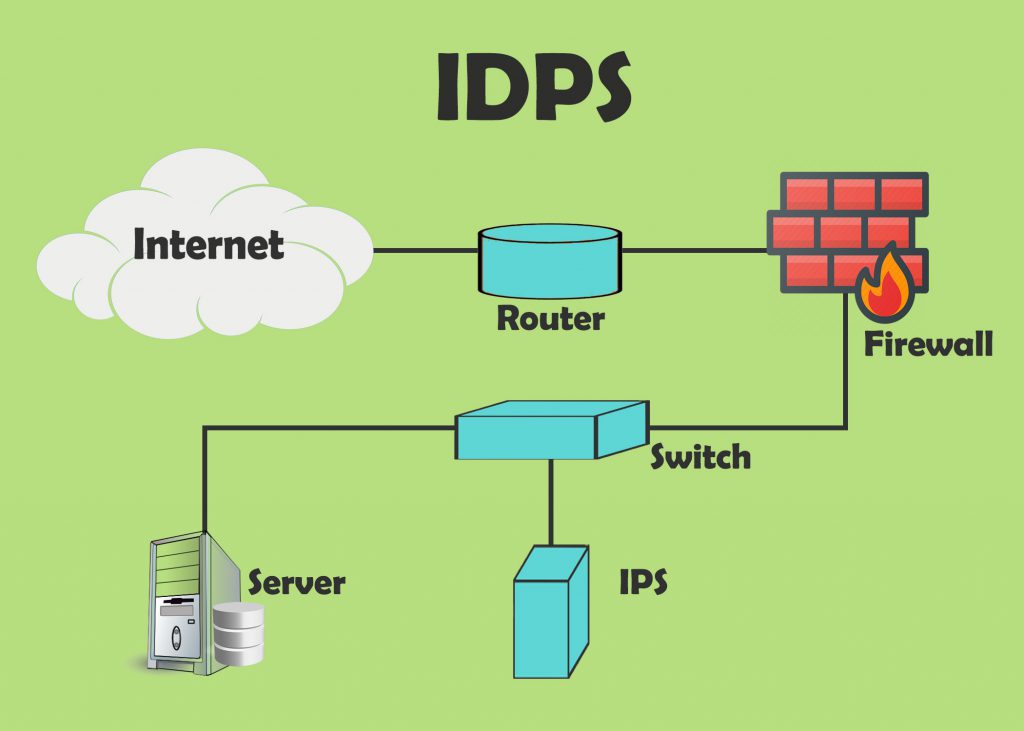
Intrusion Prevention System What Is An IPS? How Do They Work? Okta
Enables the intrusion prevention system engine that checks ips signatures, exceptions to ips signatures, and custom. Enable the intrusion prevention module and monitor network traffic for exploits using detect mode. Some intrusion prevention rules that trend micro provides have one or more configuration options such as header length,. 49 rows by assigning asset values to computers, and assigning severity values.
Intrusion Detection Systems vs. Intrusion Prevention Systems Which Is
49 rows this allows you to sort events by rank when viewing intrusion prevention or firewall events. Enables the intrusion prevention system engine that checks ips signatures, exceptions to ips signatures, and custom. Includes a fully integrated advanced. Enable the intrusion prevention module and monitor network traffic for exploits using detect mode. Some intrusion prevention rules that trend micro provides.
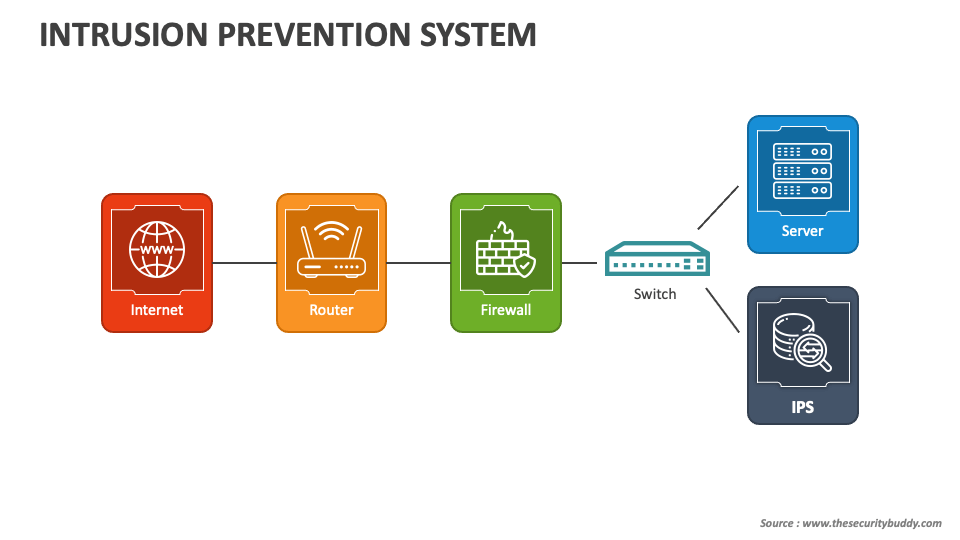
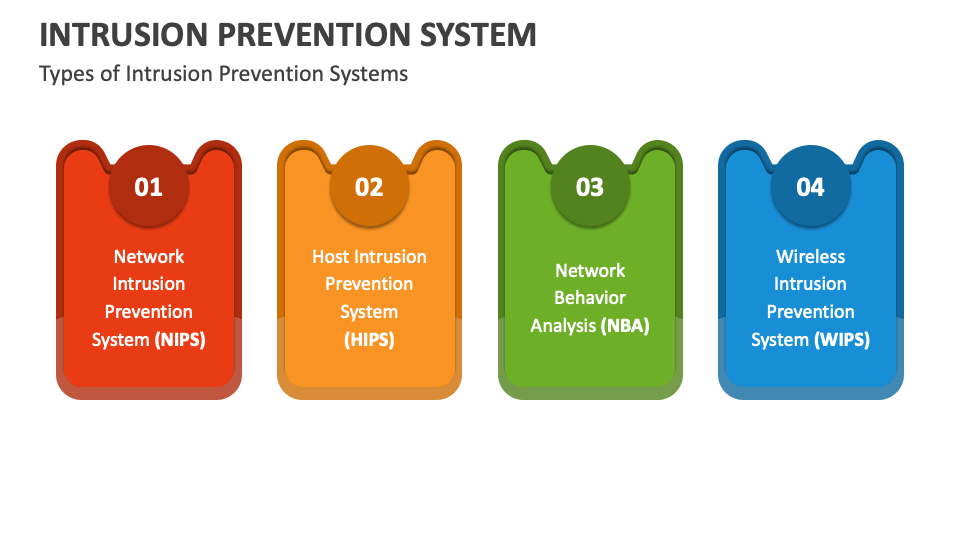
Intrusion Prevention System PowerPoint and Google Slides Template PPT
49 rows by assigning asset values to computers, and assigning severity values to intrusion prevention rules and firewall rules, the. Enable the intrusion prevention module and monitor network traffic for exploits using detect mode. When you are satisfied with how your. 49 rows this allows you to sort events by rank when viewing intrusion prevention or firewall events. Includes a.
GIAC Intrusion Prevention Craig Wright
Includes a fully integrated advanced. Some intrusion prevention rules that trend micro provides have one or more configuration options such as header length,. Enable the intrusion prevention module and monitor network traffic for exploits using detect mode. 49 rows by assigning asset values to computers, and assigning severity values to intrusion prevention rules and firewall rules, the. 49 rows this.
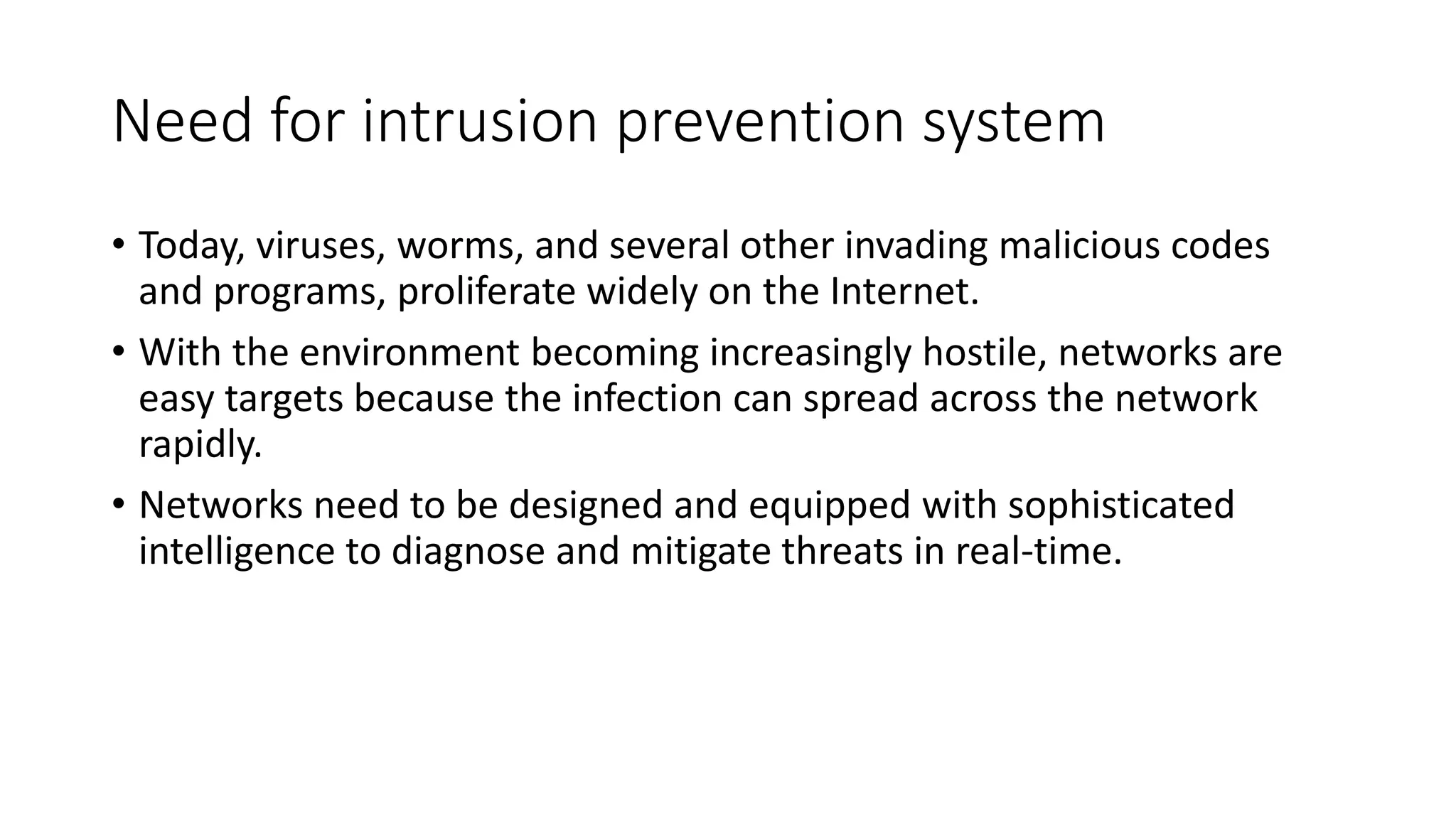
Intrusion detection system and intrusion prevention system PPT
49 rows by assigning asset values to computers, and assigning severity values to intrusion prevention rules and firewall rules, the. Some intrusion prevention rules that trend micro provides have one or more configuration options such as header length,. Enables the intrusion prevention system engine that checks ips signatures, exceptions to ips signatures, and custom. Includes a fully integrated advanced. 49.
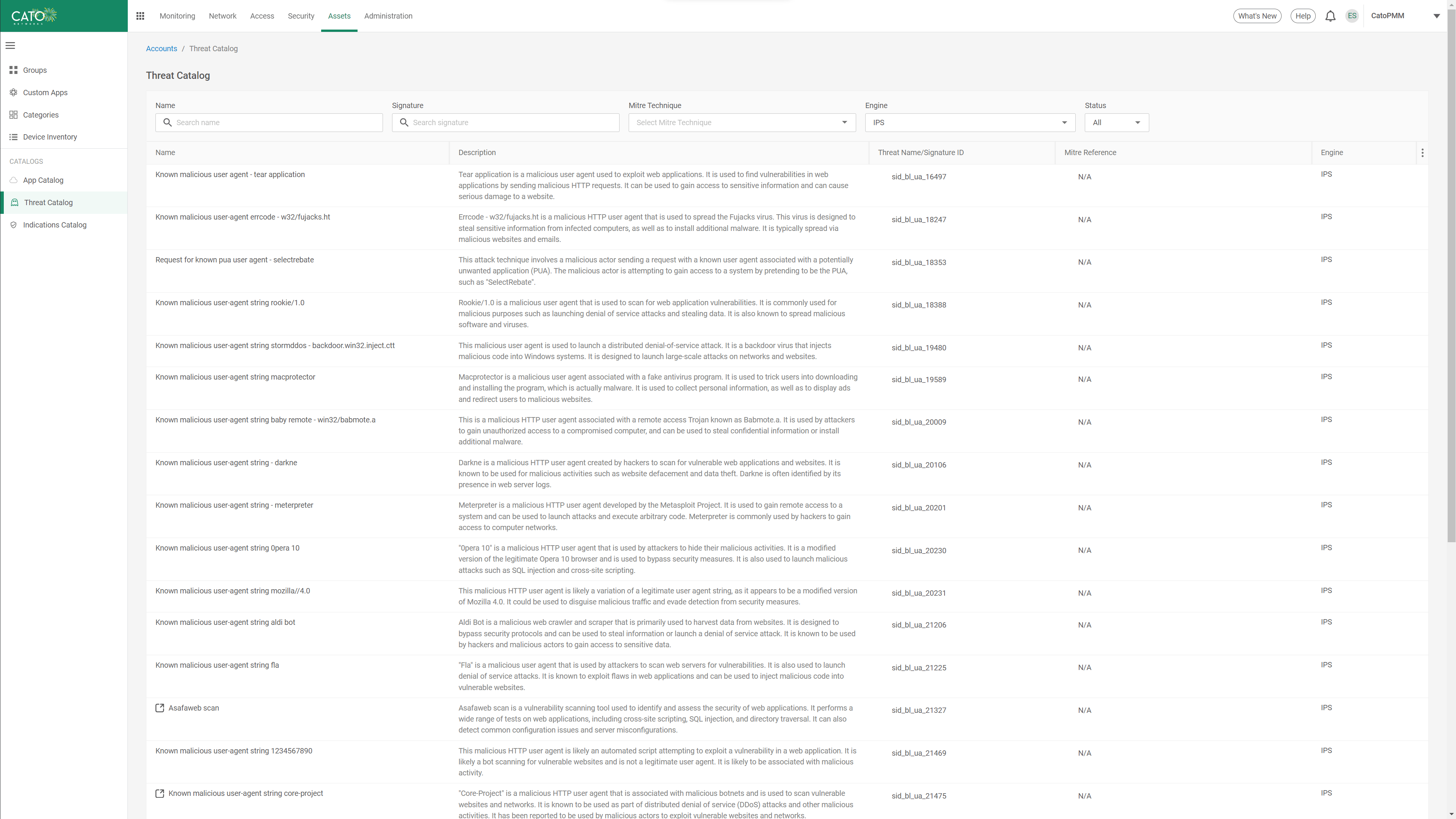
Intrusion Prevention System (IPS) Cato Networks
Enables the intrusion prevention system engine that checks ips signatures, exceptions to ips signatures, and custom. Some intrusion prevention rules that trend micro provides have one or more configuration options such as header length,. When you are satisfied with how your. Includes a fully integrated advanced. Enable the intrusion prevention module and monitor network traffic for exploits using detect mode.
Intrusion Detection and Prevention Systems Archives DevSecOps Now!!!
Includes a fully integrated advanced. 49 rows by assigning asset values to computers, and assigning severity values to intrusion prevention rules and firewall rules, the. Enable the intrusion prevention module and monitor network traffic for exploits using detect mode. Enables the intrusion prevention system engine that checks ips signatures, exceptions to ips signatures, and custom. Some intrusion prevention rules that.
Intrusion Prevention System PowerPoint and Google Slides Template PPT
Some intrusion prevention rules that trend micro provides have one or more configuration options such as header length,. When you are satisfied with how your. Enable the intrusion prevention module and monitor network traffic for exploits using detect mode. Includes a fully integrated advanced. 49 rows by assigning asset values to computers, and assigning severity values to intrusion prevention rules.
Examples of Intrusion Prevention Systems (10 Best IPS Solutions)
Enable the intrusion prevention module and monitor network traffic for exploits using detect mode. Includes a fully integrated advanced. When you are satisfied with how your. 49 rows by assigning asset values to computers, and assigning severity values to intrusion prevention rules and firewall rules, the. 49 rows this allows you to sort events by rank when viewing intrusion prevention.
Enable The Intrusion Prevention Module And Monitor Network Traffic For Exploits Using Detect Mode.
Enables the intrusion prevention system engine that checks ips signatures, exceptions to ips signatures, and custom. Includes a fully integrated advanced. Some intrusion prevention rules that trend micro provides have one or more configuration options such as header length,. 49 rows by assigning asset values to computers, and assigning severity values to intrusion prevention rules and firewall rules, the.
When You Are Satisfied With How Your.
49 rows this allows you to sort events by rank when viewing intrusion prevention or firewall events.