Regex Sql Injection Prevention - However, you could enter a very long. Search, filter and view user submitted regular expressions in the regex library. Over 20,000 entries, and counting! This cheat sheet will help you prevent sql injection flaws in your applications. Sql injection is a vulnerability and threat, with the most occurrence in a web based system. In this research we evaluate and. It will define what sql injection is, explain where those. No, your application will not be 100% secured if you use some pattern matching or regex to identify sql injection attack. Generally sql injection occurs in the strings passed to the parameters of a sql command such as insert, update, delete, or select. The regular expression threat protection policy can protect your backend apis and microservices from sql injection attacks.
Over 20,000 entries, and counting! However, you could enter a very long. In this research we evaluate and. This cheat sheet will help you prevent sql injection flaws in your applications. Generally sql injection occurs in the strings passed to the parameters of a sql command such as insert, update, delete, or select. It will define what sql injection is, explain where those. The regular expression threat protection policy can protect your backend apis and microservices from sql injection attacks. You can't invoke a command from a regex, so you can't do an sql injection in this case. No, your application will not be 100% secured if you use some pattern matching or regex to identify sql injection attack. Sql injection is a vulnerability and threat, with the most occurrence in a web based system.
In this research we evaluate and. The regular expression threat protection policy can protect your backend apis and microservices from sql injection attacks. Search, filter and view user submitted regular expressions in the regex library. It will define what sql injection is, explain where those. However, you could enter a very long. Generally sql injection occurs in the strings passed to the parameters of a sql command such as insert, update, delete, or select. You can't invoke a command from a regex, so you can't do an sql injection in this case. This cheat sheet will help you prevent sql injection flaws in your applications. No, your application will not be 100% secured if you use some pattern matching or regex to identify sql injection attack. Sql injection is a vulnerability and threat, with the most occurrence in a web based system.
An InDepth Guide to Preventing SQL Injection Attacks Through Prepared
However, you could enter a very long. No, your application will not be 100% secured if you use some pattern matching or regex to identify sql injection attack. In this research we evaluate and. The regular expression threat protection policy can protect your backend apis and microservices from sql injection attacks. Search, filter and view user submitted regular expressions in.
SQL Injection Prevention 7 Tested Ways
However, you could enter a very long. No, your application will not be 100% secured if you use some pattern matching or regex to identify sql injection attack. It will define what sql injection is, explain where those. This cheat sheet will help you prevent sql injection flaws in your applications. You can't invoke a command from a regex, so.
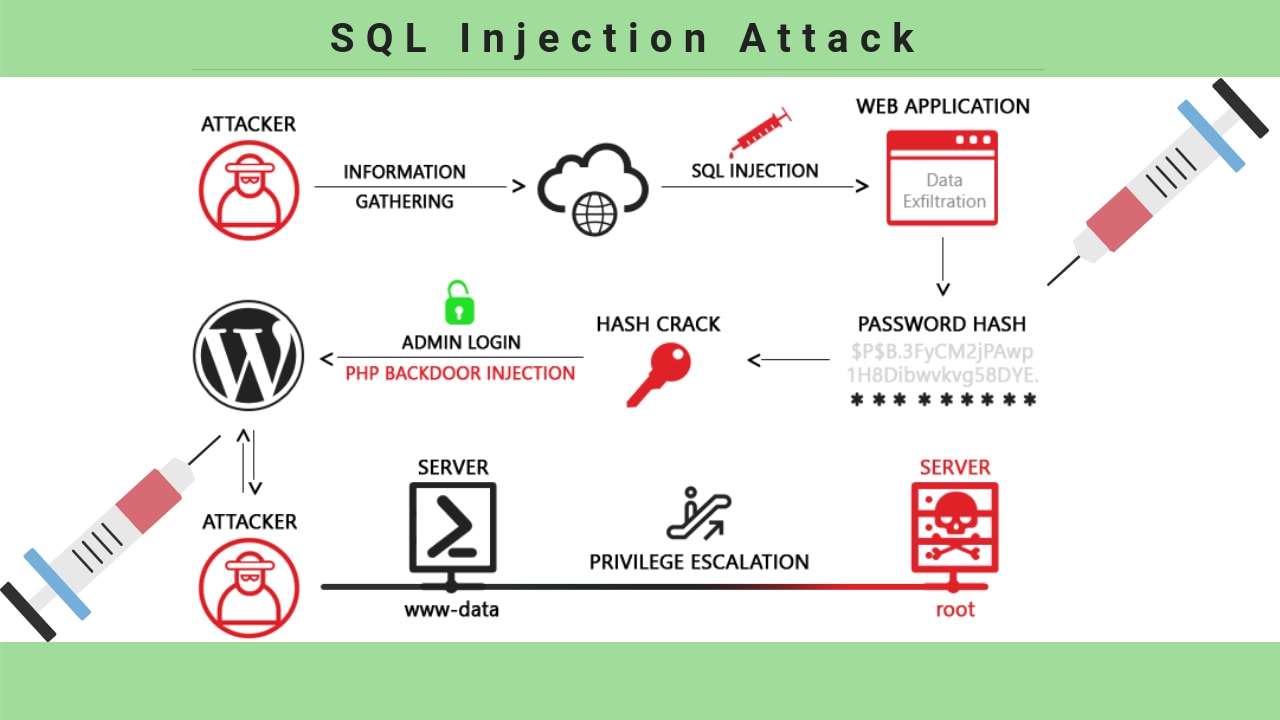
Types of SQL Injection Attack Examples Gridinsoft Blogs
Search, filter and view user submitted regular expressions in the regex library. However, you could enter a very long. Generally sql injection occurs in the strings passed to the parameters of a sql command such as insert, update, delete, or select. In this research we evaluate and. You can't invoke a command from a regex, so you can't do an.
GitHub banulalakwindu/sqlinjectionpreventionguide A practical
In this research we evaluate and. You can't invoke a command from a regex, so you can't do an sql injection in this case. Generally sql injection occurs in the strings passed to the parameters of a sql command such as insert, update, delete, or select. Sql injection is a vulnerability and threat, with the most occurrence in a web.
6 Expert Tips on SQL Injection Mitigation & Prevention Enterprise
In this research we evaluate and. This cheat sheet will help you prevent sql injection flaws in your applications. Over 20,000 entries, and counting! However, you could enter a very long. It will define what sql injection is, explain where those.
SQL Injection More Command PDF
In this research we evaluate and. No, your application will not be 100% secured if you use some pattern matching or regex to identify sql injection attack. Search, filter and view user submitted regular expressions in the regex library. Generally sql injection occurs in the strings passed to the parameters of a sql command such as insert, update, delete, or.
SQL Injection Types, Examples And Prevention, 49 OFF
Search, filter and view user submitted regular expressions in the regex library. This cheat sheet will help you prevent sql injection flaws in your applications. Generally sql injection occurs in the strings passed to the parameters of a sql command such as insert, update, delete, or select. However, you could enter a very long. Sql injection is a vulnerability and.
SQL Injection Attack Definition, Types & Prevention
Sql injection is a vulnerability and threat, with the most occurrence in a web based system. The regular expression threat protection policy can protect your backend apis and microservices from sql injection attacks. In this research we evaluate and. Search, filter and view user submitted regular expressions in the regex library. However, you could enter a very long.
SQL Injection Types, Examples And Prevention, 49 OFF
It will define what sql injection is, explain where those. The regular expression threat protection policy can protect your backend apis and microservices from sql injection attacks. Search, filter and view user submitted regular expressions in the regex library. Generally sql injection occurs in the strings passed to the parameters of a sql command such as insert, update, delete, or.
What is SQL Injection? Attack Example & Prevention Gridinsoft
Sql injection is a vulnerability and threat, with the most occurrence in a web based system. Over 20,000 entries, and counting! No, your application will not be 100% secured if you use some pattern matching or regex to identify sql injection attack. The regular expression threat protection policy can protect your backend apis and microservices from sql injection attacks. It.
No, Your Application Will Not Be 100% Secured If You Use Some Pattern Matching Or Regex To Identify Sql Injection Attack.
Over 20,000 entries, and counting! The regular expression threat protection policy can protect your backend apis and microservices from sql injection attacks. In this research we evaluate and. Search, filter and view user submitted regular expressions in the regex library.
Sql Injection Is A Vulnerability And Threat, With The Most Occurrence In A Web Based System.
This cheat sheet will help you prevent sql injection flaws in your applications. Generally sql injection occurs in the strings passed to the parameters of a sql command such as insert, update, delete, or select. However, you could enter a very long. You can't invoke a command from a regex, so you can't do an sql injection in this case.