Insider Threat Prevention - Threat detection and identification is the process by which persons who might present an insider threat risk due to their observable, concerning behaviors come to the attention of an. This approach can help an organization define specific insider. Proactively managing insider threats can stop the trajectory or change the course of events from a harmful outcome to an effective mitigation. Organizations manage insider threats through. To combat the insider threat, organizations should. The insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial governments; Through a case study approach, this guide details an actionable framework for an effective insider threat mitigation program: Defining the threat, detecting and identifying.
The insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial governments; This approach can help an organization define specific insider. Organizations manage insider threats through. Threat detection and identification is the process by which persons who might present an insider threat risk due to their observable, concerning behaviors come to the attention of an. Through a case study approach, this guide details an actionable framework for an effective insider threat mitigation program: Proactively managing insider threats can stop the trajectory or change the course of events from a harmful outcome to an effective mitigation. Defining the threat, detecting and identifying. To combat the insider threat, organizations should.
Through a case study approach, this guide details an actionable framework for an effective insider threat mitigation program: Organizations manage insider threats through. This approach can help an organization define specific insider. The insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial governments; Proactively managing insider threats can stop the trajectory or change the course of events from a harmful outcome to an effective mitigation. Defining the threat, detecting and identifying. To combat the insider threat, organizations should. Threat detection and identification is the process by which persons who might present an insider threat risk due to their observable, concerning behaviors come to the attention of an.
Insider Threats Risks, Identification and Prevention
The insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial governments; This approach can help an organization define specific insider. To combat the insider threat, organizations should. Defining the threat, detecting and identifying. Threat detection and identification is the process by which persons who might present an insider threat risk due to their observable,.
2023 Insider Threat Detection and Prevention Best Practices Sanity
Organizations manage insider threats through. The insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial governments; Through a case study approach, this guide details an actionable framework for an effective insider threat mitigation program: Proactively managing insider threats can stop the trajectory or change the course of events from a harmful outcome to an.
Insider Threat Prevention Intelligent SecOps
This approach can help an organization define specific insider. Through a case study approach, this guide details an actionable framework for an effective insider threat mitigation program: Organizations manage insider threats through. To combat the insider threat, organizations should. The insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial governments;
Insider Threat Report Crowd Research Partners
Defining the threat, detecting and identifying. The insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial governments; This approach can help an organization define specific insider. Proactively managing insider threats can stop the trajectory or change the course of events from a harmful outcome to an effective mitigation. Organizations manage insider threats through.
Insider Threat Prevention Biometrica Systems, Inc.
Threat detection and identification is the process by which persons who might present an insider threat risk due to their observable, concerning behaviors come to the attention of an. Through a case study approach, this guide details an actionable framework for an effective insider threat mitigation program: Organizations manage insider threats through. Proactively managing insider threats can stop the trajectory.
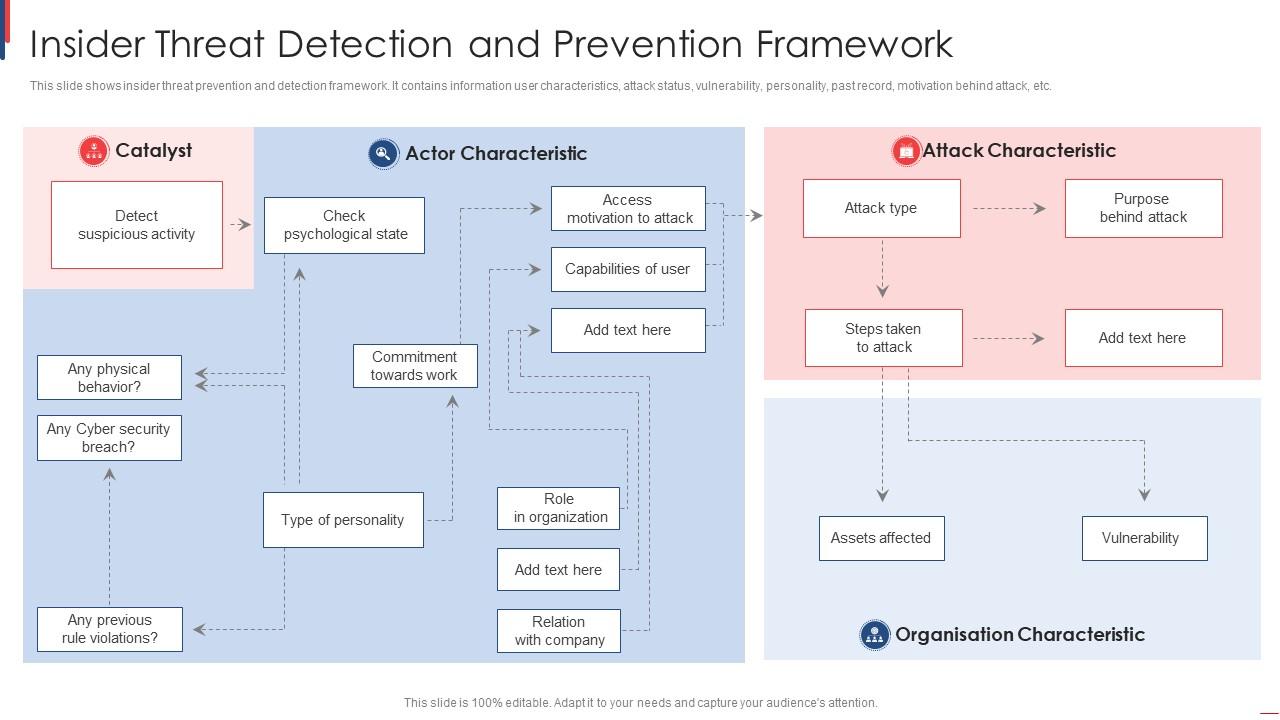
Insider Threat Detection And Prevention Framework PPT Presentation
Organizations manage insider threats through. Proactively managing insider threats can stop the trajectory or change the course of events from a harmful outcome to an effective mitigation. Through a case study approach, this guide details an actionable framework for an effective insider threat mitigation program: Threat detection and identification is the process by which persons who might present an insider.
Strengthen Security by Addressing Insider Risk CloudOptics Multi
Proactively managing insider threats can stop the trajectory or change the course of events from a harmful outcome to an effective mitigation. Defining the threat, detecting and identifying. Threat detection and identification is the process by which persons who might present an insider threat risk due to their observable, concerning behaviors come to the attention of an. This approach can.
An Ultimate Guide On Insider Threat Risks And Their Prevention AskPython
Organizations manage insider threats through. The insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial governments; Threat detection and identification is the process by which persons who might present an insider threat risk due to their observable, concerning behaviors come to the attention of an. Through a case study approach, this guide details an.
Insider Threat Archives GRA Quantum
Threat detection and identification is the process by which persons who might present an insider threat risk due to their observable, concerning behaviors come to the attention of an. This approach can help an organization define specific insider. Defining the threat, detecting and identifying. The insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial.
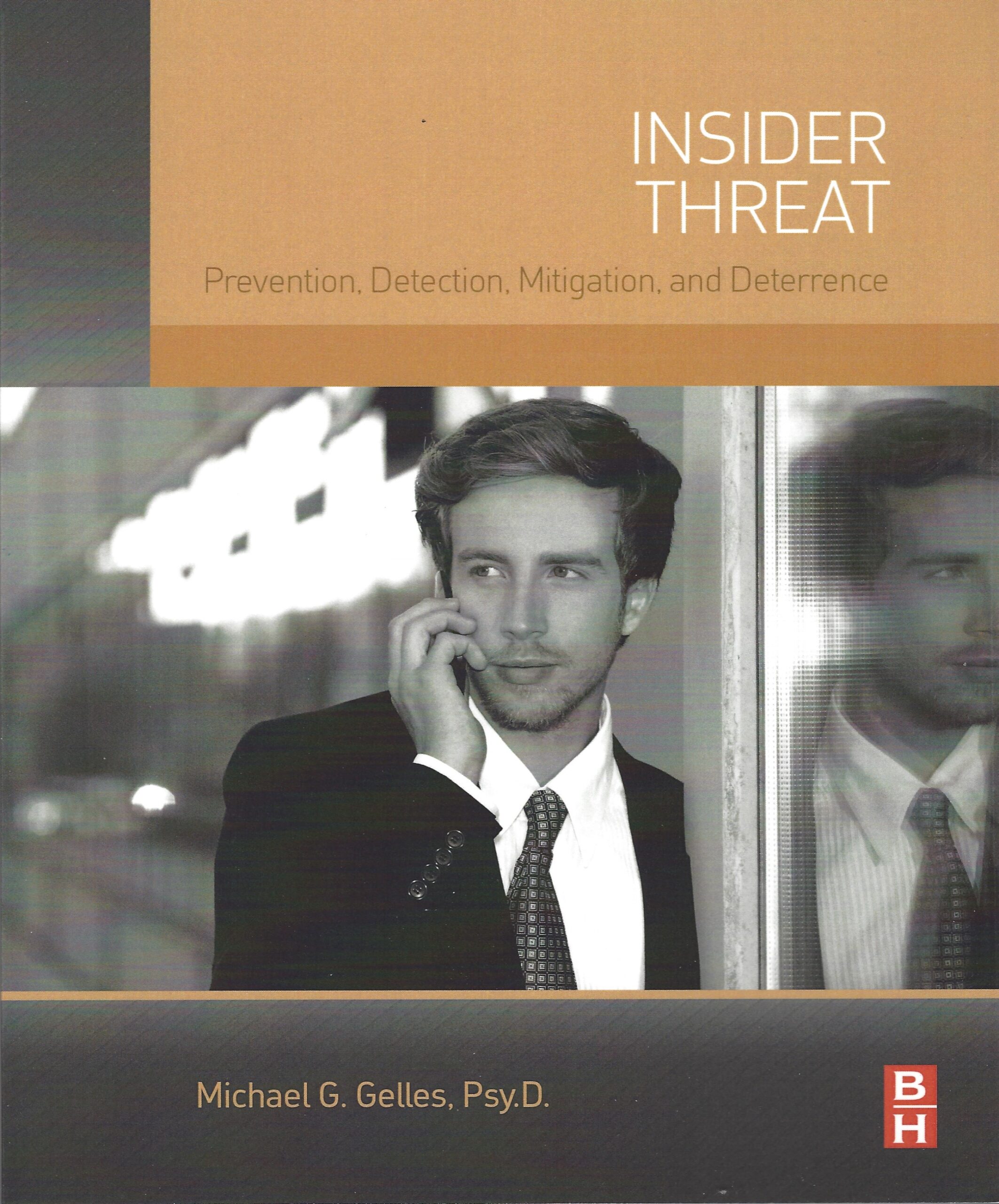
Insider Threat Prevention, Detection, Mitigation and Deterrence
Organizations manage insider threats through. This approach can help an organization define specific insider. Through a case study approach, this guide details an actionable framework for an effective insider threat mitigation program: The insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial governments; To combat the insider threat, organizations should.
Organizations Manage Insider Threats Through.
To combat the insider threat, organizations should. Defining the threat, detecting and identifying. This approach can help an organization define specific insider. Threat detection and identification is the process by which persons who might present an insider threat risk due to their observable, concerning behaviors come to the attention of an.
Proactively Managing Insider Threats Can Stop The Trajectory Or Change The Course Of Events From A Harmful Outcome To An Effective Mitigation.
Through a case study approach, this guide details an actionable framework for an effective insider threat mitigation program: The insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial governments;