Email Messages Containing Malicious File Removed After Delivery - This article explains how to use threat explorer. Identify the ip address of a malicious email sender. When it comes to computer safety, if you have no need to click on a link, and defender is telling you it is malicious, it is probably best not to poke. Start an incident for further investigation.
Start an incident for further investigation. When it comes to computer safety, if you have no need to click on a link, and defender is telling you it is malicious, it is probably best not to poke. This article explains how to use threat explorer. Identify the ip address of a malicious email sender.
Start an incident for further investigation. Identify the ip address of a malicious email sender. This article explains how to use threat explorer. When it comes to computer safety, if you have no need to click on a link, and defender is telling you it is malicious, it is probably best not to poke.
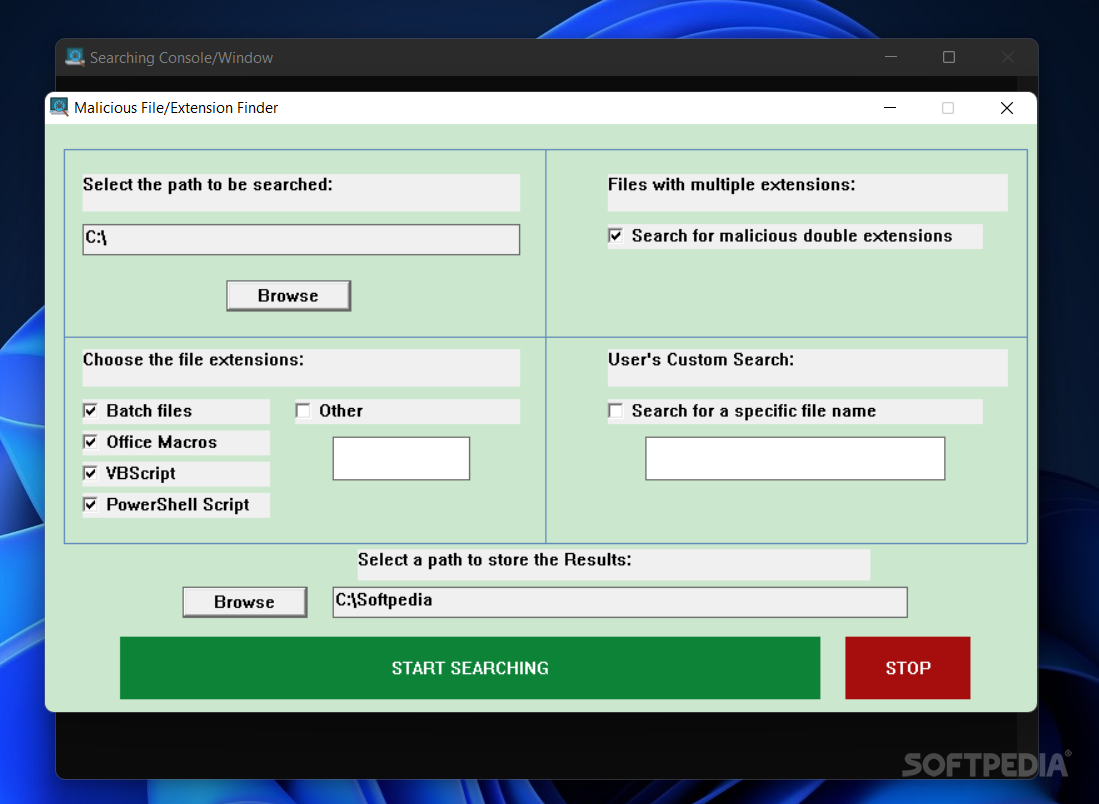
Malicious Extension/File Finder 1.0 Download, Review, Screenshots
When it comes to computer safety, if you have no need to click on a link, and defender is telling you it is malicious, it is probably best not to poke. Start an incident for further investigation. Identify the ip address of a malicious email sender. This article explains how to use threat explorer.
Detects Malicious Email Attachments To Avoid Malware DroidCops
When it comes to computer safety, if you have no need to click on a link, and defender is telling you it is malicious, it is probably best not to poke. Identify the ip address of a malicious email sender. Start an incident for further investigation. This article explains how to use threat explorer.
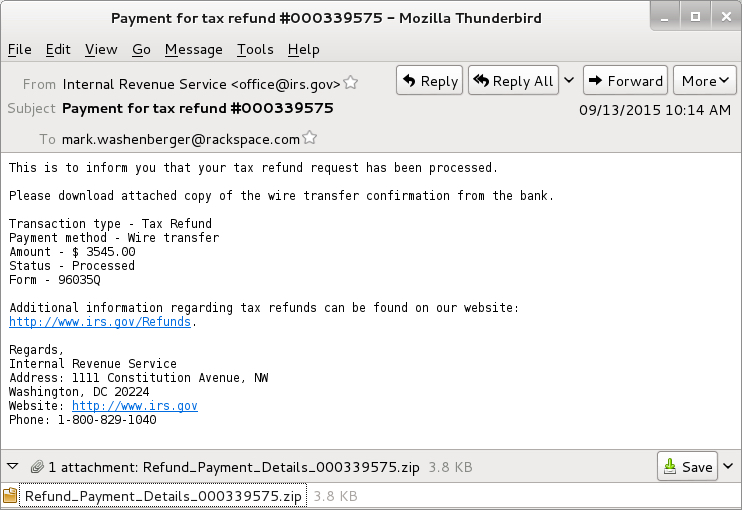
Email containing ‘payment advice note’ delivers malicious payload
Identify the ip address of a malicious email sender. This article explains how to use threat explorer. Start an incident for further investigation. When it comes to computer safety, if you have no need to click on a link, and defender is telling you it is malicious, it is probably best not to poke.
Messages containing malicious entity not removed after delivery r
This article explains how to use threat explorer. Identify the ip address of a malicious email sender. When it comes to computer safety, if you have no need to click on a link, and defender is telling you it is malicious, it is probably best not to poke. Start an incident for further investigation.
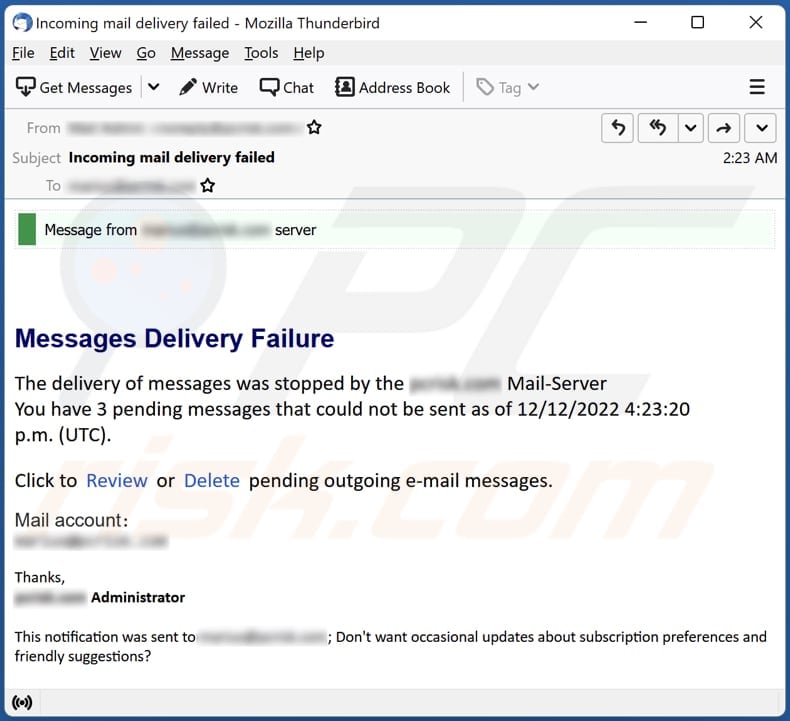
Messages Delivery Failure Email Scam Removal and recovery steps (updated)
Start an incident for further investigation. This article explains how to use threat explorer. Identify the ip address of a malicious email sender. When it comes to computer safety, if you have no need to click on a link, and defender is telling you it is malicious, it is probably best not to poke.
Malicious RTF File (CVE202321716) Protection OPSWAT
When it comes to computer safety, if you have no need to click on a link, and defender is telling you it is malicious, it is probably best not to poke. This article explains how to use threat explorer. Identify the ip address of a malicious email sender. Start an incident for further investigation.
I’ve Clicked On a Malicious Link or File, What Now? IT Consulting
This article explains how to use threat explorer. When it comes to computer safety, if you have no need to click on a link, and defender is telling you it is malicious, it is probably best not to poke. Identify the ip address of a malicious email sender. Start an incident for further investigation.
Phishing/Malicious messages going through containing html attachments
This article explains how to use threat explorer. Identify the ip address of a malicious email sender. When it comes to computer safety, if you have no need to click on a link, and defender is telling you it is malicious, it is probably best not to poke. Start an incident for further investigation.
Phishing/Malicious messages going through containing html attachments
Start an incident for further investigation. When it comes to computer safety, if you have no need to click on a link, and defender is telling you it is malicious, it is probably best not to poke. Identify the ip address of a malicious email sender. This article explains how to use threat explorer.
Malicious spam with zip attachments containing .js files SANS
When it comes to computer safety, if you have no need to click on a link, and defender is telling you it is malicious, it is probably best not to poke. Start an incident for further investigation. Identify the ip address of a malicious email sender. This article explains how to use threat explorer.
Start An Incident For Further Investigation.
This article explains how to use threat explorer. Identify the ip address of a malicious email sender. When it comes to computer safety, if you have no need to click on a link, and defender is telling you it is malicious, it is probably best not to poke.